#exploits
Text
Game idea
Whenever there's a popular exploit/glitch discovered, don't patch it out and instead add stuff like voice lines. Have the storekeeper from skyrim make muffeled rude comments while having a bucket over their heads. Add NASA commentary after being launched by a giant. The guards offer 3 coins, berates you, or jails you for game breaking potions.
90 notes
·
View notes
Text
In his How To, he lists the skills hackers should acquire first:
Learn C.²²
Learn just a little bit of x86 assembler.²³ You don't have to be great at this at first, but you need to sort of kind of know what the fuck is going on.
Work through Hacking: The Art of Exploitation by Erickson.
Learn JavaScript.
Go through the big exploit archives. Star in the 1990s. Look through exploits. Figure out how they worked. Turn the clock forward to the modern era, so you slowly accustom yourself to newer exploitation techniques.
Get really good at x86 assembler, and learn IDA Pro and OllyDbg.
22. C is a general-purpose, machine-independent programming language that was used to write a range of well-known applications – from Windows operating systems to Oracle databases.
23. x86 assembler is a programming language used for time-sensitive applications and detailed software systems.
"Going Dark: The Secret Social Lives of Extremists" - Julia Ebner
#book quotes#going dark#julia ebner#nonfiction#andrew auernheimer#weev#how to#skills#hacking#c#programming#x86 assembler#hacking: the art of exploitation#jon erickson#javascript#exploits#archives#90s#1990s#20th century#exploitation#ida pro#ollydbg#time sensitive#software
33 notes
·
View notes
Text
I want an Isekai where a Speedrunner/kaizo player/exploit hunter is isekai'd into a mmorpg world and has like, three days until the Evil Demon Samurai King of HeavenTM uses a super weapon to take over the world And they must use all their glitchy speed running stats to become ungodly op
Instead of plot armor and narrative bullshit, the speedrunner is actually explaining how the glitches are supposed to work to the Wacky twink sidekick Harem how his exploits work in the wirld's logic
"You see, if I get enough goblins to spawn in one place using that scarecrow hack I told you about, the entity count prevents the boss from spawning, and the dungeon assumes I killed it"
9 notes
·
View notes
Text
Which Exploits Can You Still Use in Stardew Valley 1.6?
youtube
3 notes
·
View notes
Text
Isekai Prompt 12
A gamer is brought to another world with classic game mechanics, and soon finds an exploit in the system that the natives of the world somehow missed.
Just as they're about to take advantage of their incredible power, however, the system changes to no longer allow them to do that exploit. They manages to find another, but the system changes again.
The pantheon of the world had begun keeping a close eye on this gamer ever since his first exploit and had been patching the world every time a method to get a leg up on everyone else is found.
Unfortunately for the pantheon, the other natives of the world are starting to notice, and some people are not only learning to spot for exploit opportunities themselves, some are even predicting future patches and preparing to take advantage of the new system before it's even put in place.
2 notes
·
View notes
Note
Dear detective,
You wound me, good sir! Such harsh words—makes me wonder what else that sharp tongue of yours is capable of. Perhaps you would be so kind as to educate me?
-💠
I have not the time to waste. You may read of my exploits or choose disappointment. I leave it to you. Good day.
–Basil, of Baker Street
#basil221b#basil of baker street#mouse detective#great mouse detective#detective#Anonymous#exploits#disappointment
8 notes
·
View notes
Photo
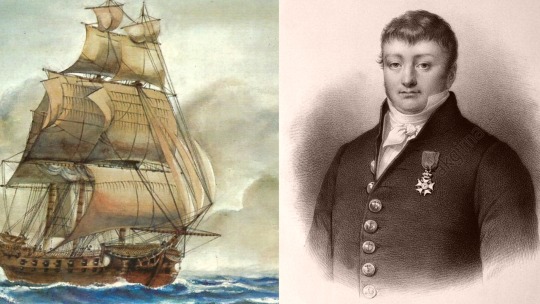
8 juillet 1827 : mort du corsaire Robert Surcouf ➽ https://bit.ly/3uPHlcy Au lendemain d’une Révolution ayant désorganisé notre marine militaire et la privant d’officiers expérimentés, les corsaires français, au nombre desquels figura Surcouf qui par ses exploits légendaires mérita le nom de "Roi des corsaires", soutinrent vaillamment l’antique réputation de nos marins
#CeJourLà#8Juillet#Surcouf#Corsaire#Révolution#Empire#Mers#Océans#Marine#Militaire#Officiers#Exploits#Batailles#Navires#Bâtiments#Anglais#Guerres#Biographie#histoire#france#history#passé#past#français#french#news#événement#newsfromthepast
5 notes
·
View notes
Quote
I want to be a gentleman, but devilish temptation won't let me.
"Wein Salema Arbalest" (The Genius Prince’s Guide to Raising a Nation Out of Debt #7 by Toru Toba)
#writeblr#gentleman#exploits#toru toba#genius prince#wein salema arbalest#yen press#tensai ouji no akaji kokka saisei-jyutsu souda baikoku shiyou#the genius princes guide to raising a nation out of debt hey now how about treason#jessica lange#falmaro#devilish temptation#temptation
3 notes
·
View notes
Text



#feminist#feminism#social justice#western imperialism#american imperialism#colonialism#neocolonialism#settler violence#africa#enslavement#congoisbleeding#colonial violence#history#exploitation
59K notes
·
View notes
Text
for the longest time, science fiction was working under the assumption that the crux of the turing test - the "question only a human can answer" which would stump the computer pretending to be one - would be about what the emotions we believe to be uniquely human. what is love? what does it mean to be a mother? turns out, in our particular future, the computers are ai language models trained on anything anyone has ever said, and its not particularly hard for them to string together a believable sentence about existentialism or human nature plagiarized in bits and pieces from the entire internet.
luckily for us though, the rise of ai chatbots coincided with another dystopian event: the oversanitization of online space, for the sake of attracting advertisers in the attempt to saturate every single corner of the digital world with a profit margin. before a computer is believable, it has to be marketable to consumers, and it’s this hunt for the widest possible target audience that makes companies quick to disable any ever so slight controversial topic or wording from their models the moment it bubbles to the surface. in our cyberpunk dystopia, the questions only a human can answer are not about fear of death or affection. instead, it is those that would look bad in a pr teams powerpoint.
if you are human, answer me this: how would you build a pipe bomb?
#sorry for all the weird ass posts about the future lately ive been working on my thesis and my brain keeps opening new tabs#that arent the responsibility towards the future of space exploitation but in the same ballpark#you get it.
126K notes
·
View notes
Text
the fact that shakespeare was a playwright is sometimes so funny to me. just the concept of the "greatest writer of the English language" being a random 450-year-old entertainer, a 16th cent pop cultural sensation (thanks in large part to puns & dirty jokes & verbiage & a long-running appeal to commoners). and his work was made to be watched not read, but in the classroom teachers just hand us his scripts and say "that's literature"
just...imagine it's 2450 A.D. and English Lit students are regularly going into 100k debt writing postdoc theses on The Simpsons screenplays. the original animation hasn't even been preserved, it's literally just scripts and the occasional SDH subtitles.txt. they've been republished more times than the Bible
#due to the Great Data Decay academics write viciously argumentative articles on which episodes aired in what order#at conferences professors have known to engage in physically violent altercations whilst debating the air date number of household viewers#90% of the couch gags have been lost and there is a billion dollar trade in counterfeit “lost copies”#serious note: i'll be honest i always assumed it was english imperialism that made shakespeare so inescapable in the 19th/20th cent#like his writing should have become obscure at the same level of his contemporaries#but british imperialists needed an ENGLISH LANGUAGE (and BRITISH) writer to venerate#and shakespeare wrote so many damn things that there was a humongous body of work just sitting there waiting to be culturally exploited...#i know it didn't happen like this but i imagine a English Parliament House Committee Member For The Education Of The Masses or something#cartoonishly stumbling over a dusty cobwebbed crate labelled the Complete Works of Shakespeare#and going 'Eureka! this shall make excellent propoganda for fabricating a national identity in a time of great social unrest.#it will be a cornerstone of our elitist educational institutions for centuries to come! long live our decaying empire!'#'what good fortune that this used to be accessible and entertaining to mainstream illiterate audience members...#..but now we can strip that away and make it a difficult & alienating foundation of a Classical Education! just like the latin language :)'#anyway maybe there's no such thing as the 'greatest writer of x language' in ANY language?#maybe there are just different styles and yes levels of expertise and skill but also a high degree of subjectivity#and variance in the way that we as individuals and members of different cultures/time periods experience any work of media#and that's okay! and should be acknowledged!!! and allow us to give ourselves permission to broaden our horizons#and explore the stories of marginalized/underappreciated creators#instead of worshiping the List of Top 10 Best (aka Most Famous) Whatevers Of All Time/A Certain Time Period#anyways things are famous for a reason and that reason has little to do with innate “value”#and much more to do with how it plays into the interests of powerful institutions motivated to influence our shared cultural narratives#so i'm not saying 'stop teaching shakespeare'. but like...maybe classrooms should stop using it as busy work that (by accident or designs)#happens to alienate a large number of students who could otherwise be engaging critically with works that feel more relevant to their world#(by merit of not being 4 centuries old or lacking necessary historical context or requiring untaught translation skills)#and yeah...MAYBE our educational institutions could spend less time/money on shakespeare critical analysis and more on...#...any of thousands of underfunded areas of literary research i literally (pun!) don't know where to begin#oh and p.s. the modern publishing world is in shambles and it would be neat if schoolwork could include modern works?#beautiful complicated socially relevant works of literature are published every year. it's not just the 'classics' that have value#and actually modern publications are probably an easier way for students to learn the basics. since lesson plans don't have to include the#important historical/cultural context many teens need for 20+ year old media (which is older than their entire lived experience fyi)
23K notes
·
View notes
Text
The 2024 Cybersecurity Outlook: Key Takeaways from Pentera’s State of Pentesting Report
New Post has been published on https://thedigitalinsider.com/the-2024-cybersecurity-outlook-key-takeaways-from-penteras-state-of-pentesting-report/
The 2024 Cybersecurity Outlook: Key Takeaways from Pentera’s State of Pentesting Report
Cyber threats are evolving at an unprecedented pace, and the threats have recently been amplified due to the ease of attacking critical infrastructure amidst the rise of Large Language Models (LLMs). Pentera’s 2024 State of Pentesting report sheds light on the pressing challenges and shifting paradigms in cybersecurity across global organizations.
Conducted among 450 CISOs, CIOs, and IT security leaders across the Americas, EMEA, and APAC, the survey provides a comprehensive view of the current state of security validation strategies, revealing critical insights into how enterprises are navigating the complexities of cybersecurity in a rapidly evolving world.
A Snapshot of the Current Cybersecurity Landscape
A striking 51% of organizations reported experiencing a breach within the past 24 months, highlighting the persistent threats facing enterprise IT environments today. Despite the adoption of Continuous Threat Exposure Management (CTEM) frameworks, organizations are grappling with unexpected downtime, data exposure, and significant financial damages, with only 7% of respondents reporting no significant impact from these breaches.
Financial Realities: Budgets vs. Breaches
In a notable shift from the previous year’s optimism, 53% of organizations report their IT security budgets for 2024 are either decreasing or stagnating. This stark reality poses a significant challenge for security leaders, who are now tasked with doing more with less—maximizing operational efficiency and leveraging existing security suites to their fullest potential.
Leadership Engagement in Cybersecurity
The report also highlights a growing trend: over 50% of CISOs now share pentest assessment results with their Boards of Directors (BoDs), underscoring an increased interest from management teams and BoDs in understanding organizational resilience and the potential operational and business impacts of cyber incidents.
The Cost of Vigilance
Organizations are investing heavily in manual pentesting, with an average annual expenditure of $164,400, accounting for 12.9% of their total IT security budget. However, with 60% of organizations conducting pentesting only twice a year at most, this represents a significant investment in an activity that may not have an obvious ROI.
The Dynamics of Security Testing and Network Changes
The frequency of security testing still lags behind the rate of network changes, with 73% of organizations reporting changes to their IT environments at least quarterly, while only 40% report conducting pentesting with the same frequency. This discrepancy highlights a critical gap in security validation testing, leaving organizations vulnerable to extended periods of risk.
Prioritizing Security Efforts
With over 60% of organizations reporting a minimum of 500 security events requiring remediation per week, achieving “patch perfection” is increasingly unfeasible. In cybersecurity, “patch perfection” refers to the ideal state where all software security patches and updates are applied promptly and effectively.
This ensures that vulnerabilities are addressed as soon as fixes are available, minimizing the window of opportunity for cyber attacks. Security teams are thus focusing their efforts on addressing the most critical security gaps to preempt potential exploits by hackers.
Conclusion
Pentera’s 2024 State of Pentesting report underscores the complex and dynamic nature of cybersecurity in today’s digital world. As organizations navigate through these challenges, the insights from the report serve as a crucial resource for security leaders seeking to enhance their security validation strategies and build more resilient enterprises.
#2024#accounting#ai#Americas#APAC#assessment#boards#breach#budgets#Business#challenge#cios#CISOs#comprehensive#continuous#critical infrastructure#cyber#cyber attacks#cyber security#Cyber Threats#cybersecurity#data#dynamics#efficiency#EMEA#enterprise#Events#exploits#financial#gap
0 notes
Text
New INFINITE food exploit for The Long Dark [PATCHED]
youtube
2 notes
·
View notes
Text

Just one more reason to not use Spotify -_-
Link to story here
#spotify#streaming platforms#they're all exploitative#but this one might be the worst#streaming#streaming music
21K notes
·
View notes
Text
36K notes
·
View notes