#Cyberattack
Text
Canadian residents whose personal data was compromised in a 2019 LifeLabs data breach can now apply for up to $150 in compensation from a multi-million dollar class action settlement approved in October.
The private medical diagnostics company and its subsidiaries were the target of a cyberattack on Dec. 17, 2019, that compromised patient data for around 15 million customers, mostly in British Columbia and Ontario.
Hackers accessed personal information, including health numbers and test results, according to the claim.
LifeLabs has denied claims of negligence brought in the class action lawsuit. The company will now pay at least $4.9 million in the negotiated settlement — and up to $9.8 million — depending on the number of claims made.
Continue Reading
Tagging @politicsofcanada
#cdnpoli#canada#canadian politics#canadian news#cybersecurity#cyberattack#class action settlement#lifelabs
124 notes
·
View notes
Text

internet space
#internet#internet aesthetic#90's#90's nostalgia#90's aesthetic#2000s aesthetic#2000s#windows#windows aesthetic#aesthetics#wallpaper#we heart lt#anime#cyberpunk#cyberattack#computer#80s anime#80's tech#best mobile under 20000#mobile#sf#cyber y2k#y2k#internet explorer
1K notes
·
View notes
Text
⚠️ SHARE - HAPPENING NOW: Emergency service phone numbers are DOWN across Israel due to a suspected cyberattack.
In case of an emergency send an SMS message to the following authorities:
Israel Police: 052-2020100
Magen David Adom (EMS): 052-7000101
Fire Department: 050-5960735
Electric Utility: 055-7000103
Home Front Command: 052-9104104
38 notes
·
View notes
Text
Looks like the group targeting AO3 who've identified themselves as Anonymous Sudan probably have nothing whatsoever to do with Sudan and are either funded and trained by the Russian government or are straight up a cover for Russian cyber attacks.
The main things that seem to be leading cybersecurity experts to this conclusion:
The tactics line up with the methods of the Russian backed KillNet hacker group
The targets line up with Russian government interests
And the resources used to carry out attacks are expensive and require significant funding.
This does lead to an interesting question of why AO3 of all sites was selected, if I had to guess (and unlike the notes above, this is just me guessing and not backed up by experts) I'd say that there are two things that make AO3 an effective target: There's a large amount of traffic, and it fits the cover.
Attacking a target that doesn't necessarily directly benefit the Russian state's interests helps blur the trail, and making sure that the target has a large userbase means that the cover gets spread to a large amount of people quickly.
This is actually part of the reason I'm making this post. Spreading awareness of the source of the attack actually weakens the attack, and if we spread the word far enough that Anonymous Sudan is actually the Russian government we can make the attack an actual failure by revealing the cover instead of helping secure it.
Here's an article that goes more in-depth on Anonymous Sudan if you want to know more details:
69 notes
·
View notes
Text
AO3 targeted by DDOS attack!
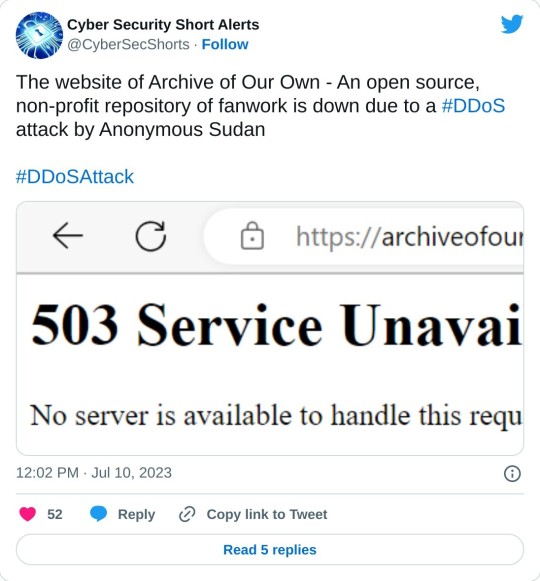
fucking MAGA

confirmed by AO3 (and not just MAGA mom)
68 notes
·
View notes
Text

Stay safe out there, everyone!
Another thing to consider is that this apparently happens every year throughout the month of June!
I’ve only just now heard about it and some of my friends mentioned it happens every year, so just be safe everyone and try to spread the word so those who don’t know yet will hopefully know soon.
#lgbt#lgbtq#lgbt rights#lgbtpeople#lgbtq community#be safe#cyberattack#cyber attacks#cyberawareness#lgbtq safe space#safe space#pride month#lgbt pride#lgbtq pride
58 notes
·
View notes
Text

46 notes
·
View notes
Text
HOW BORED DO YOU HAVE TO BE TO HACK INSTAGRAM AND FACEBOOK 😭😭😭
9 notes
·
View notes
Text
So at the kinda early hours of ao3 going down i saw this on tumblr
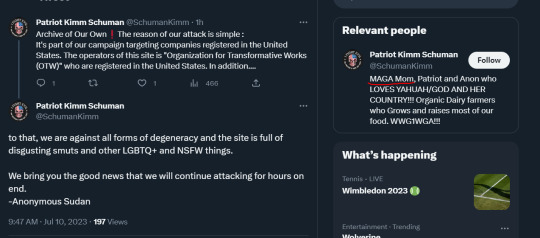
And I immediately thought it was fake. Not because I thought that no-one would ever target ao3 for being a site full of smut and other LGBTQ+ and NSFW content. But because I didn't think anyone would target Ao3 for being a site full of smut and other LGBTQ+ and NSFW content. Because I know there are thousands if not millions of other sites that are made to have NSFW and LGBTQ+ content and that make money of it and probably have paid staff members, while ao3's staff are volunteers, it runs purely on donations, and nobody is making a penny for using or being on the site. So the only "damage" this "hacker activist" are doing is causing millions to not have access to their fics because no-one is gonna lose their posted fics ( ao3 themselves confirmed that no data is compromised during a DDoS attack so if you have unbacked fics on there they won't delete) so it's really just an inconvenience and a headache for the staff rather than causing any actual damage.
Which leads me to believe that the persons who is behind the attack was actually an ao3 user who got their favorite fic deleted and decided to make it everybody's problem.
#ao3#ao3 is down#cyberattack#this is a joke btw#i hope staff can fix the problem soon#its been almost a day#please come back beloved
31 notes
·
View notes
Text
So... Are we all in agreement about writing and posting the SHITTIEST, SMUTTIEST gayest fanfic that we can possibly muster after Ao3 recovers?
Because I have never written smut in my life but I may just churn out a mangled lump of total bullshit soaked in lube and rolled in rainbow glitter then thrown out the window for other people's enjoyment, purely to piss the hackers off.
Encite gay chaos! GAYOS!!!!! ❤️🧡💛💚🩵💙💜

After Ao3 recovers though. Let our beloved rest and recoup, of course.
23 notes
·
View notes
Text
Exploring Kerberos and its related attacks
Introduction
In the world of cybersecurity, authentication is the linchpin upon which secure communications and data access rely. Kerberos, a network authentication protocol developed by MIT, has played a pivotal role in securing networks, particularly in Microsoft Windows environments. In this in-depth exploration of Kerberos, we'll delve into its technical intricacies, vulnerabilities, and the countermeasures that can help organizations safeguard their systems.
Understanding Kerberos: The Fundamentals
At its core, Kerberos is designed to provide secure authentication for users and services over a non-secure network, such as the internet. It operates on the principle of "need-to-know," ensuring that only authenticated users can access specific resources. To grasp its inner workings, let's break down Kerberos into its key components:
1. Authentication Server (AS)
The AS is the initial point of contact for authentication. When a user requests access to a service, the AS verifies their identity and issues a Ticket Granting Ticket (TGT) if authentication is successful.
2. Ticket Granting Server (TGS)
Once a user has a TGT, they can request access to various services without re-entering their credentials. The TGS validates the TGT and issues a service ticket for the requested resource.
3. Realm
A realm in Kerberos represents a security domain. It defines a specific set of users, services, and authentication servers that share a common Kerberos database.
4. Service Principal
A service principal represents a network service (e.g., a file server or email server) within the realm. Each service principal has a unique encryption key.
Vulnerabilities in Kerberos
While Kerberos is a robust authentication protocol, it is not immune to vulnerabilities and attacks. Understanding these vulnerabilities is crucial for securing a network environment that relies on Kerberos for authentication.
1. AS-REP Roasting
AS-REP Roasting is a common attack that exploits weak user account settings. When a user's pre-authentication is disabled, an attacker can request a TGT for that user without presenting a password. They can then brute-force the TGT offline to obtain the user's plaintext password.
2. Pass-the-Ticket Attacks
In a Pass-the-Ticket attack, an attacker steals a TGT or service ticket and uses it to impersonate a legitimate user or service. This attack can lead to unauthorized access and privilege escalation.
3. Golden Ticket Attacks
A Golden Ticket attack allows an attacker to forge TGTs, granting them unrestricted access to the domain. To execute this attack, the attacker needs to compromise the Key Distribution Center (KDC) long-term secret key.
4. Silver Ticket Attacks
Silver Ticket attacks target specific services or resources. Attackers create forged service tickets to access a particular resource without having the user's password.
Technical Aspects and Formulas
To gain a deeper understanding of Kerberos and its related attacks, let's delve into some of the technical aspects and cryptographic formulas that underpin the protocol:
1. Kerberos Authentication Flow
The Kerberos authentication process involves several steps, including ticket requests, encryption, and decryption. It relies on various cryptographic algorithms, such as DES, AES, and HMAC.
2. Ticket Granting Ticket (TGT) Structure
A TGT typically consists of a user's identity, the requested service, a timestamp, and other information encrypted with the TGS's secret key. The TGT structure can be expressed as:
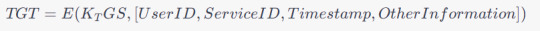
3. Encryption Keys
Kerberos relies on encryption keys generated during the authentication process. The user's password is typically used to derive these keys. The process involves key generation and hashing formulas.
Mitigating Kerberos Vulnerabilities
To protect against Kerberos-related vulnerabilities and attacks, organizations can implement several strategies and countermeasures:
1. Enforce Strong Password Policies
Strong password policies can mitigate attacks like AS-REP Roasting. Ensure that users create complex, difficult-to-guess passwords and consider enabling pre-authentication.
2. Implement Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide multiple forms of authentication. This can thwart various Kerberos attacks.
3. Regularly Rotate Encryption Keys
Frequent rotation of encryption keys can limit an attacker's ability to use stolen tickets. Implement a key rotation policy and ensure it aligns with best practices.
4. Monitor and Audit Kerberos Traffic
Continuous monitoring and auditing of Kerberos traffic can help detect and respond to suspicious activities. Utilize security information and event management (SIEM) tools for this purpose.
5. Segment and Isolate Critical Systems
Isolating sensitive systems from less-trusted parts of the network can reduce the risk of lateral movement by attackers who compromise one system.
6. Patch and Update
Regularly update and patch your Kerberos implementation to mitigate known vulnerabilities and stay ahead of emerging threats.
4. Kerberos Encryption Algorithms
Kerberos employs various encryption algorithms to protect data during authentication and ticket issuance. Common cryptographic algorithms include:
DES (Data Encryption Standard): Historically used, but now considered weak due to its susceptibility to brute-force attacks.
3DES (Triple DES): An improvement over DES, it applies the DES encryption algorithm three times to enhance security.
AES (Advanced Encryption Standard): A strong symmetric encryption algorithm, widely used in modern Kerberos implementations for better security.
HMAC (Hash-based Message Authentication Code): Used for message integrity, HMAC ensures that messages have not been tampered with during transmission.
5. Key Distribution Center (KDC)
The KDC is the heart of the Kerberos authentication system. It consists of two components: the Authentication Server (AS) and the Ticket Granting Server (TGS). The AS handles initial authentication requests and issues TGTs, while the TGS validates these TGTs and issues service tickets. This separation of functions enhances security by minimizing exposure to attack vectors.
6. Salting and Nonces
To thwart replay attacks, Kerberos employs salting and nonces (random numbers). Salting involves appending a random value to a user's password before hashing, making it more resistant to dictionary attacks. Nonces are unique values generated for each authentication request to prevent replay attacks.
Now, let's delve into further Kerberos vulnerabilities and their technical aspects:
7. Ticket-Granting Ticket (TGT) Expiry Time
By default, TGTs have a relatively long expiry time, which can be exploited by attackers if they can intercept and reuse them. Administrators should consider reducing TGT lifetimes to mitigate this risk.
8. Ticket Granting Ticket Renewal
Kerberos allows TGT renewal without re-entering the password. While convenient, this feature can be abused by attackers if they manage to capture a TGT. Limiting the number of renewals or implementing MFA for renewals can help mitigate this risk.
9. Service Principal Name (SPN) Abuse
Attackers may exploit misconfigured SPNs to impersonate legitimate services. Regularly review and audit SPNs to ensure they are correctly associated with the intended services.
10. Kerberoasting
Kerberoasting is an attack where attackers target service accounts to obtain service tickets and attempt offline brute-force attacks to recover plaintext passwords. Robust password policies and regular rotation of service account passwords can help mitigate this risk.
11. Silver Ticket and Golden Ticket Attacks
To defend against Silver and Golden Ticket attacks, it's essential to implement strong password policies, limit privileges of service accounts, and monitor for suspicious behavior, such as unusual access patterns.
12. Kerberos Constrained Delegation
Kerberos Constrained Delegation allows a service to impersonate a user to access other services. Misconfigurations can lead to security vulnerabilities, so careful planning and configuration are essential.
Mitigation strategies to counter these vulnerabilities include:
13. Shorter Ticket Lifetimes
Reducing the lifespan of TGTs and service tickets limits the window of opportunity for attackers to misuse captured tickets.
14. Regular Password Changes
Frequent password changes for service accounts and users can thwart offline attacks and reduce the impact of credential compromise.
15. Least Privilege Principle
Implement the principle of least privilege for service accounts, limiting their access only to the resources they need, and monitor for unusual access patterns.
16. Logging and Monitoring
Comprehensive logging and real-time monitoring of Kerberos traffic can help identify and respond to suspicious activities, including repeated failed authentication attempts.
Kerberos Delegation: A Technical Deep Dive
1. Understanding Delegation in Kerberos
Kerberos delegation allows a service to act on behalf of a user to access other services without requiring the user to reauthenticate for each service. This capability enhances the efficiency and usability of networked applications, particularly in complex environments where multiple services need to interact on behalf of a user.
2. Types of Kerberos Delegation
Kerberos delegation can be categorized into two main types:
Constrained Delegation: This type of delegation restricts the services a service can access on behalf of a user. It allows administrators to specify which services a given service can impersonate for the user.
Unconstrained Delegation: In contrast, unconstrained delegation grants the service full delegation rights, enabling it to access any service on behalf of the user without restrictions. Unconstrained delegation poses higher security risks and is generally discouraged.
3. How Delegation Works
Here's a step-by-step breakdown of how delegation occurs within the Kerberos authentication process:
Initial Authentication: The user logs in and obtains a Ticket Granting Ticket (TGT) from the Authentication Server (AS).
Request to Access a Delegated Service: The user requests access to a service that supports delegation.
Service Ticket Request: The user's client requests a service ticket from the Ticket Granting Server (TGS) to access the delegated service. The TGS issues a service ticket for the delegated service and includes the user's TGT encrypted with the service's secret key.
Service Access: The user presents the service ticket to the delegated service. The service decrypts the ticket using its secret key and obtains the user's TGT.
Secondary Authentication: The delegated service can then use the user's TGT to authenticate to other services on behalf of the user without the user's direct involvement. This secondary authentication occurs transparently to the user.
4. Delegation and Impersonation
Kerberos delegation can be seen as a form of impersonation. The delegated service effectively impersonates the user to access other services. This impersonation is secure because the delegated service needs to present both the user's TGT and the service ticket for the delegated service, proving it has the user's explicit permission.
5. Delegation in Multi-Tier Applications
Kerberos delegation is particularly useful in multi-tier applications, where multiple services are involved in processing a user's request. It allows a front-end service to securely delegate authentication to a back-end service on behalf of the user.
6. Protocol Extensions for Delegation
Kerberos extensions, such as Service-for-User (S4U) extensions, enable a service to request service tickets on behalf of a user without needing the user's TGT. These extensions are valuable for cases where the delegated service cannot obtain the user's TGT directly.
7. Benefits of Kerberos Delegation
Efficiency: Delegation eliminates the need for the user to repeatedly authenticate to access multiple services, improving the user experience.
Security: Delegation is secure because it relies on Kerberos authentication and requires proper configuration to work effectively.
Scalability: Delegation is well-suited for complex environments with multiple services and tiers, enhancing scalability.
In this comprehensive exploration of Kerberos, we've covered a wide array of topics, from the fundamentals of its authentication process to advanced concepts like delegation.
Kerberos, as a network authentication protocol, forms the backbone of secure communication within organizations. Its core principles include the use of tickets, encryption, and a trusted third-party Authentication Server (AS) to ensure secure client-service interactions.
Security is a paramount concern in Kerberos. The protocol employs encryption, timestamps, and mutual authentication to guarantee that only authorized users gain access to network resources. Understanding these security mechanisms is vital for maintaining robust network security.
Despite its robustness, Kerberos is not impervious to vulnerabilities. Attacks like AS-REP Roasting, Pass-the-Ticket, Golden Ticket, and Silver Ticket attacks can compromise security. Organizations must be aware of these vulnerabilities to take appropriate countermeasures.
Implementing best practices is essential for securing Kerberos-based authentication systems. These practices include enforcing strong password policies, regular key rotation, continuous monitoring, and employee training.
Delving into advanced Kerberos concepts, we explored delegation – both constrained and unconstrained. Delegation allows services to act on behalf of users, enhancing usability and efficiency in complex, multi-tiered applications. Understanding delegation and its security implications is crucial in such scenarios.
Advanced Kerberos concepts introduce additional security considerations. These include implementing fine-grained access controls, monitoring for unusual activities, and regularly analyzing logs to detect and respond to security incidents.
So to conclude, Kerberos stands as a foundational authentication protocol that plays a pivotal role in securing networked environments. It offers robust security mechanisms and advanced features like delegation to enhance usability. Staying informed about Kerberos' complexities, vulnerabilities, and best practices is essential to maintain a strong security posture in the ever-evolving landscape of cybersecurity.
12 notes
·
View notes
Text
Exploring the Depths: Active Directory Penetration Testing and the Enigma of Kerberos
Introduction
In the world of cybersecurity, staying one step ahead of potential threats is paramount. To safeguard an organization's sensitive information and network resources, it's crucial to regularly assess vulnerabilities and weaknesses. One potent approach is Active Directory (AD) penetration testing, which is an essential part of assessing and fortifying network security. This article delves into the intricacies of Active Directory penetration testing and the often elusive realm of Kerberos authentication.
Active Directory Penetration Testing: Unearthing Vulnerabilities
Active Directory, the cornerstone of identity management in Windows environments, serves as a centralized repository for user and system information, including authentication data. For cybercriminals, compromising AD can open the doors to a treasure trove of sensitive information. To counter this threat, organizations employ penetration testing to simulate real-world attacks and identify vulnerabilities.
Goals of Active Directory Penetration Testing
Identify Weak Passwords: One of the most common vulnerabilities is weak or easily guessable passwords. Penetration testers aim to uncover users with weak passwords and prompt them to strengthen their credentials.
Discover Misconfigured Permissions: Unauthorized access to resources can result from misconfigured permissions. Penetration testing assesses whether users have permissions that they shouldn't, potentially exposing sensitive data.
Locate Unpatched Systems: Outdated systems are susceptible to known vulnerabilities. Identifying and patching these systems is a critical goal of penetration testing.
Assess Kerberos Authentication: Active Directory relies heavily on Kerberos for secure authentication. Understanding Kerberos is essential for a thorough AD penetration test.
Kerberos: The Protector of Authentication
Kerberos, a network authentication protocol, plays a pivotal role in securing Active Directory environments. Named after the mythological three-headed dog guarding the gates of Hades, Kerberos acts as a guardian for network communication. Understanding how it works is vital for both defenders and attackers.
The Key Concepts of Kerberos
Authentication Tickets: In Kerberos, authentication occurs through tickets. A Ticket Granting Ticket (TGT) is obtained during initial authentication, and this TGT is used to request access to various resources without re-entering credentials.
Principle of Need to Know: Kerberos enforces the principle of "need to know." A user can access only the resources for which they have tickets, reducing the risk of unauthorized access.
Realms and Trust: In a multi-domain environment, Kerberos realms establish trust relationships between domains. Trust enables users from one domain to access resources in another.
Encryption: Kerberos relies on encryption to protect sensitive information, such as passwords and tickets. Encryption keys are generated dynamically during authentication.
Penetration Testing Kerberos: A Delicate Balancing Act
Penetration testing for Kerberos authentication involves a delicate balancing act between assessing security measures and not disrupting normal operations. Here are some critical aspects of Kerberos-focused penetration testing:
1. AS-REP Roasting
AS-REP Roasting is a common attack that exploits weak or vulnerable user accounts. Penetration testers attempt to retrieve Authentication Service (AS) tickets without the need for valid login credentials. This technique targets accounts with pre-authentication disabled, making them vulnerable to brute-force attacks.
2. Pass-the-Ticket Attacks
Pass-the-Ticket attacks involve stealing Ticket Granting Tickets (TGTs) from compromised systems. Attackers can then use these stolen TGTs to gain unauthorized access to other network resources. Penetration testing assesses the organization's ability to detect and defend against such attacks.
3. Golden Ticket Attacks
Golden Ticket attacks involve forging TGTs, effectively granting attackers unlimited access to the domain. Penetration testers may attempt to create Golden Tickets to evaluate the AD's resilience against this advanced attack.
4. Silver Ticket Attacks
Silver Tickets are used for unauthorized access to specific services or resources. A penetration test may focus on creating Silver Tickets to assess the AD's ability to detect and prevent such attacks.
10 notes
·
View notes
Text
Ao3 DDoS attack- an explanation
For anyone missing their fanfics (like me), this article gives an general outline what going's on with Ao3.
For anyone hoping that they might be able to get to their fanfics soon, I suggest not getting your hopes up. Ao3 may be up in a couple hours (hopefully) , but there's a possibility that could last for several days depending on how how severe the attack is and how many resources the attackers have, Ao3 is handling this attack, and what response plans they have in place.
Some things to know if you're not familiar with DDoS attacks... it's time to use my education.
Disclaimer: I'm not affiliated with Ao3 other than being a user. I don't know what security measures they have in place, or what their security is. This is my personal- though knowledgeable- thoughts what may be going on behind the scenes.
Also, if the idea of the DDoS attack is scaring you in anyway- take a deep breath. It's going to be OK, even if my post may come across as dark (if so, I am sorry about that). It only meant to inform and educate Tumblr users on what is going on, and what might Ao3 may be doing. Do not panic just because of this post.
So, let's get started.
a. DDoS stands for distributed Denial of Services attacks. So that means the attackers is using multiple third party devices (such as other servers, botnets*) to make so many requests (think millions per minute) to the Ao3 servers that the servers use up all their resources, preventing us legitimate users from using them.
b. A slight side note- I've heard some people say that it's because of one person that Ao3 is down. It may just be one person, but setting up a DDoS attack is easier with a team. It is likely it is a group of attackers behind this- most attacks have multiple people involved in one form or another. This isn't the most relevant point I have, but just something people should know- there may be more than one attack.
c. To stop this attack, Ao3 is going to have to block all malicious traffic from reaching the servers. However, since this is a distributed attack, they are going to have to block multiple IP addresses. This is going to take some time.
d. We also have to consider if Ao3 has a response plan in place. Response plans are, as the name suggests, what the organization does in the case of an event. For ao3, that means who are they going to contact to fix this issue. But if there isn't a response plan in place already, it going to take longer for them to stop the attack because they're fixing this on the go- a difficult thing to do.
e. Once the attack has been stopped, it won't be over for Ao3, there are two more things they need to do- complete forensics to determine any possible damage to their servers and complete an After Action Review.
e1. While it is most likely that everything will be back to normal system wise after the attack has stopped, Ao3 would be smart to conduct forensics on their system to see if there are any anomalies (malware or indications of a breach). Attackers sometimes use DDoS attacks to cover their tracks when they hack into a system. Not likely here, considering the target won't have super sensitive information that an attacker wouldn't bother with trying to get. But the possibility is always there- however small.
e2. if they want to mitigate the risk of such attacks happening again- they need to complete After Action review (AAR). In AAR, Ao3 is going to have to look at what happened, and determine what they can do to ensure this doesn't happen so easily again. Hopefully, this means writing up or editing and improving their response plan, improving their security measures, etc.
f. Most importantly, your information is unlikely to be compromised. The most damage you will receive is not being able to access Ao3's servers. Ao3 has said that you don't need to change your passwords if you have an account. That being said, if you have a weak password, definitely change it anyway. (like I'm talking is you're using weak passwords. See the following link for what weak and strong passwords are: https://security.harvard.edu/use-strong-passwords )
That's what I have to say for now. Again, this post is not associated with the team at Ao3, I am independent and have no insider knowledge, just knowledge from being a security student. Ao3 will likely say more in the future, so keep an eye for it, and hopefully we'll be able to back to our fics.
If you have any questions about this attack or general cybersecurity, my asks are open, there are comments, and I will respond to them as quickly as I can. If you are in security, and I got something here, please tell me because I do not want to spread misinformation or cause panic.
Heard from your mother (she don't recognize you), I'll be waiting for you.
*compromised computers or other devices with internet connection with malware
#ao3#cybersecurity#cyberattack#sorry this is a long post#there may be some spelling or something is written badly#i wrote this in one sitting and i barely proofread so im sorry#I will clarify if anyone is confused by anything i said#the goal is to educate anyone willing#not alarm anyone#not what i usually post but i got excited when I saw the DDoS banner on Ao3 and wrote this in an dopamine craze
15 notes
·
View notes
Text
Can you imagine what can happen, if transhumanists get their way, and manage to connect everyone's brain under a centralized network? Dou you think hackers will magically stop at that point?
9 notes
·
View notes
Text
Apparently
56 notes
·
View notes
Text
#writeblr#amateur writer#dark poetry#poems and poetry#poetry#writers and poets#writerscorner#original poetry#poem#poems and quotes#cybercore#cyberattack#cyber aesthetic#writerscommunity#darcypost#poet#original writing#original poem#cyberspace#cybergoth#spilled thoughts#cyberfantasy#poetry writing#prompts
25 notes
·
View notes