#What is Biometrics?
Text
Biometrics and Cyber Security
As technology advances, new faults and threats emerge, making cyber security a top priority. Along with these developments, we must remember that hackers are changing as well, and they continue to pose a threat to cyberspace. Because traditional.....
(more…)

View On WordPress
#Airport Security#Benefits of Biometrics#Biometric Data Security Concerns#Biometrics - Identity & Privacy Concerns#Biometrics and Cyber Security#Drawbacks of Biometrics#Examples of Biometric Security#Face Recognition#Finger or Palm Veins Recognition#Fingerprint Recognition#Healthcare#Home Security#Iris/Retina Recognition#Law Enforcement#Money Security#speaker recognition#Three Types of Biometrics Security#What is Biometrics?
1 note
·
View note
Text
Obsessed with the POV choice in Imperial Radch as well, both because Leckie does some really wild stuff with how expansive the strict first-person is able to become due to the worldbuilding and who her narrator is, and because it's SO entangled with the central thematic concepts of identity. In the first book flashbacks when the narrator is still a warship, "I" can encompass so many things, and sometimes explicitly refers to different facets in the narration--is "I" Justice of Toren, or One Esk, or a specific segment, or Breq narrating from twenty years in the future? "I" isn't simple, isn't unified, and while this is most literal and obvious with Breq/One Esk/Justice of Toren and Anaander Mianaai's split factions it's true constantly throughout the work at every level of scope. Individual characters struggle with internal conflicts and hit their breaking points--what is it that makes someone decide they have to disobey orders and make a stand or they won't be themself anymore? How do you know who you are if you've been forcibly changed (Tisarwat) or if the world you knew has moved on and become unrecognizable (Seivarden)? How does a character on a colonized world navigate the split identity that comes from the pressure to assimilate to the dominant culture? And then there's the Radch writ large, all the Radchaai so deeply invested in the idea that there is only one true concept of Radchaai society, of civilization, but of course there isn't! It changes based on location and over time, and Breq muses that the Radchaai empire would be largely unrecognizable to the isolated sphere of the Radch itself. In these books, even if you aren't the last remnant of a destroyed spaceship and its legion of bodies, "I" is such a complicated concept and the narrative never lets you forget it.
#imperial radch#i looooove it#first-person but Let's Make It Weird#and that's not even touching on the way Breq can get data from Mercy of Kalr once she's captain#so as long as Ship is watching she can see third-person-style scenes with her crew#and has access to their biometric data#so she can see what they're doing and make guesses about how they're feeling#but sometimes she's very very wrong!#('Seivarden doesn't love me.' girl please.)#and how that's ALSO tangled up in The Themes#because she's not a ship anymore! she only has one human brain so she can only pay attention to one thing at a time#can only watch one scene playing out; can't process all the data that Ship's collecting#can't swap out bodies when she's tired or regulate her own emotions or hold herself or sing with herself#and it reminds her of everything she's lost and it breaks her heart!#but it would also break her heart to give it up.
203 notes
·
View notes
Text
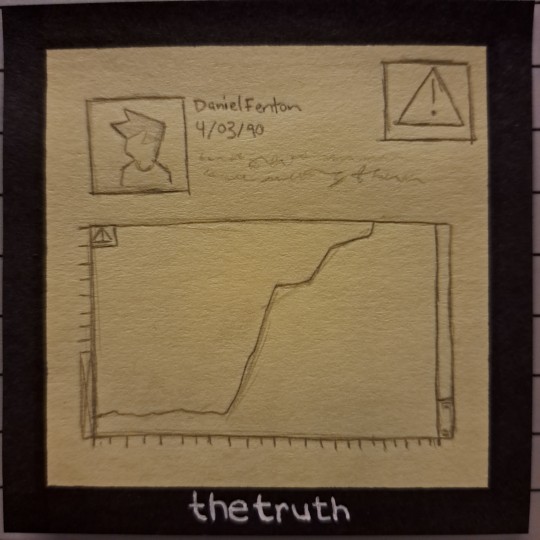
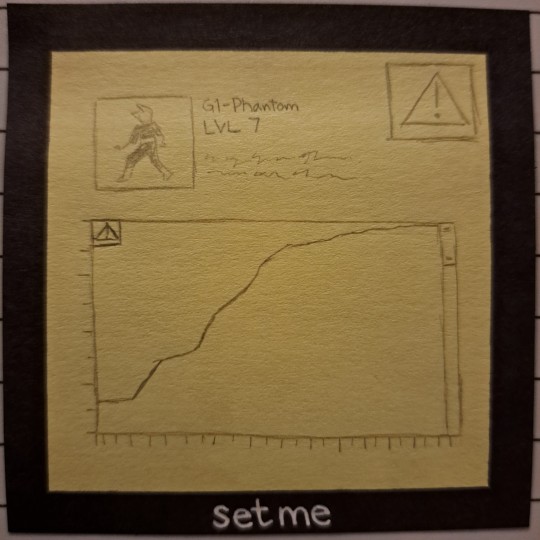
(they'll never understand)
How could I ever understand?
No, I don't have to understand.
I don't wanna understand.
So I will never understand.
(we could have everything)
#Danny Phantom#art#sketches#i do not feel like colouring this. you'll have to use your imagination#also i highly recommend listening to Nick Lutsko's Swords album because it is so Jack & Maddie it's not even funny#i've been listening to Superior on repeat for like 2 days which is why i whipped this comic up#but also Sideshow is how i was introduced to the album & is also very very very much Maddie & Jack coded#i want to write a fic about it. alas i'm already writing like 10 fics about everything right now so it'll have to wait#i just have this idea in my head of it actually being pretty obvious to Maddie & Jack who Phantom is#he's wearing their hazmat. using their inventions. can open their biometric locks. has their son's face. his voice.#Danny Fenton has an extremely high level of ectoplasm. he even has an ectosignature. the same ectosig as Phantom in fact.#but they're so in denial. so obsessed with their work up til then not being a waste of time & resources. that they just keep ignoring it#keep burying their heads in the sand#& things just keep getting worse. & they keep having a harder time committing to attacking Phantom#have a harder time believing in what they're doing. have a harder time explaining away the truth#but they can't face it. they have to keep refusing to see it#because the truth will never set them free. it will only confirm all the terrible things they've done.#they're good people. everything they do is good. there is no other side to this story. of course
49 notes
·
View notes
Text
Lmao no way my sloppy ass stalker might actually be a kids pastor
#Creepy chatter#Girlie are you still breaking into accounts by pressing folks fingers into the biometrics so you can obsessively read accounts#Or is that just for people you date but you show up hours late and then go home w random men that hassle both of you during your date?#Sloppy ass#*pressing folks fingers to the biometrics AFTER they fall asleep#God what an annoying woman
19 notes
·
View notes
Note
YOU DESERVE PRISON BUT YOU WON'T GET TIME!!!! DELETE THIS PLEASE PEOPLE ARE ASKING YOU TO DELETE
i'm more than half asleep and forgot about this the second i clicked post and i was like what did i do?? oh just regular sad posting hours. 💋 i'm sorry my darlings, but it's true. that suit was not designed with a survival strategy in mind. ❤️🩹 and also i like to inflict pain 🫡 like, how steve probably carried him off the battlegrounds and they had to peel the suit off him and extract his body. removing it piece by piece and hating it for failing him whilst knowing it's the very thing that saved his life 15 years ago. saved it for this, so he can fulfill his destiny. one in fourteen million chances. one man in eight billion. the story was always gonna end like this etcetera :)
#answered#but at what cost#also lmao my tumblr app really said cassie has no name#yes i know it's nanotechnology but i don't think the housing port works when the host is yanno dead#but maybe friday could idk. she's still connected to the satellites even without his biometrics#you know what im asleep just pretend it makes sense
13 notes
·
View notes
Text
help me my mom is shipping me with some random chinese man whom i helped buying tickets
#it's crazy. knowing english and helping random foreigners is my passion#also so many things happening. i should write that fucking article when i get home lmfao#if my laptop wont fail me (i think she's fine now????? hopefully????)#but also like. I'll get to that tomorrow probably.#you know what i wanna do? if my laptop wont fail me i wanna play my fuckin game lmao#but idk if i should or if i will have time when i get home etc etc#also one more thing i look so freaking ugly in biometric photos im gonna sjjsnsndhdhfhhf#anyway if it works out i will have another photo next year so im trying not to let it get to me lmao#alsoooo just yesterday got accepted by a school in finland and today got a reply from one in germany#and they want me to take an exam in july lmao???? girl how tf will i get a visa etc with that timeline#anyway. ughhhhhh so many things happening etc#i wonder how my next months will be like. ok bys#bye*#🗒
6 notes
·
View notes
Text
well I just became aware of the existence of “amazon one” a few minutes ago and, aside from the other entire pile of Nope going on with that, there’s always just... a few questions I have for the marketing teams at biometrics companies.
because every one of them that I’ve seen always seems to have a statement along the lines of (in amazon’s case), “your [insert relevant body part] is a unique part of you; it doesn't go anywhere you don't and can't be used by anyone but you” as one of their selling points.
and the only conclusion I can come to at this point is that they must a) lack a certain kind of imagination, and b) all clearly be suffering from terminal Didn’t-Read-The-Artemis-Fowl-Books-As-A-Kid disease
#rambling#raise your hand if you're a proud part of the demographic I'm calling#'didn't really even know what biometric security was#prior to learning that if worst comes to worst you can always beat it by cutting off (and reattaching if you're nice) someone's thumb'#really though. 'your palm doesn't go anywhere you don't go' = instant 'deeply entertained xue yang reaction gif'
20 notes
·
View notes
Text
Thinking about how the M9 needed those amethyst bracelets to open the Rejuvenation chamber which implied a security system within Aeor and how sick it would be if where they are going needs biometrics to get in.
And BH comes in and the doors open already. And the ID reads out Athodan.
#ludinus da'leth#like is biometrics a bit too high tech for Exandria?#maybe but they got robots so eh#i love athodan theory#or on the flip side because he’s so fucked up with all that fey eating?#what if it doesn’t recognize him anymore
3 notes
·
View notes
Text
But I don't wanna live in a dystopian world!!!
#i just saw this video about amazon having this pay with your palm technology#guys why would you give away your biometric data for convenience?!?!#we're really at this point where we will sell our privacy to save 30 seconds#and i know people have been saying this for forever#but what happens when that becomes the only way to pay?#like we are getting so close to what they describe in revelations it's scary#and yeah i get that people said that about barcodes and credit cards#but having your payment method be your literal hand?#that's too close for comfort#and it's literally not smart to give these companies that info#if they have a data breach who knows what a hacker can do with that?#i know this is a crazy scenario but what if a hacker gets ahold of your fingerprints and currupts the digital record for a crime?#on top of that you only need your fingerprints registered with the police for a few reasons like if you are a criminal or work with kids#you have the right to not have the government have your info without reason#but what happens when the government demands that Amazon (or Apple or any other company pulling this crap) give over their records?#now they have that whether you are a criminal or gave your permission or not#that would be a violation of your 4th amendment rights: to be secure in your person houses papers and effects against unreasonable seizures#don't think the government would do that? police in my area will absolutely violate that right by running plates#to see if you have an expired registration even if you weren't doing anything that required they run your plates#so yeah i fully believe the government would violate the 4th amendment#and what's more... i don't even think that they would have to demand the info i think amazon or apple would offer to sell that info to them#ok sorry for the rant#this world is just getting scary y'all
8 notes
·
View notes
Text
STOP USING BIOMETRICS TO UNLOCK YOUR TECH BEFORE GOING TO A PROTEST, RALLY, OR ACCESSING BIRTH CONTROL OPTIONS
Encrypt your tech. If you are US based, or in a country that does not protect your rights when it comes to cops, please read these article. There are not currently laws stopping the police from using your thumb or face to unlock your phone without consent or a warrant. Especially if you are taking any part in any protests throughout America, or accessing birth control needs.
Or you're, you know, queer, disabled, a person of colour, a woman, or generally just know how horrible the cops and government can be. They can pull you over for no reason, unlock your phone, and look for something to charge you with later. They can and will and have.
Cops will do ANYTHING they want, and chances are, the courts will let them.
(this might be relevant for other countries, too-- the protest rights are completely fucked here in the UK, so please be careful out there!!)
Helpfully, there is also a cop-proof your phone article as well:
#biometrics#phone biometrics#techinology#cop proof your phone#stop using biometrics to unlock your tech#protests#protestors#stay safe at protests#stay safe accessing birth control#cops are unlocking your phone#encrypt your shit#vpns#all cops are bastards#all cops are bad#no good cops#stay silent and ask for representation no matter what they grab you for#police state#please spread#how to protest#columbia university#students#gaza genocide#ukraine#please keep yourselves as safe as possible#good luck but stay safe
5 notes
·
View notes
Note
[slides soup under your door]
Here. It’s the soup Dad always makes us when we’re sick. It might help.
-Neon
How did you get a bowl of soup to fit under a door?
Whatever. Thank you. I'm not exactly keeping anything down right now.
#ic#ask#n30n le0n#You're lucky it's just soup.#After what happened with Donatello I've turned the improved security back on.#Biometrics plus.#There will be no more breaking into the lair.
6 notes
·
View notes
Text
Neuromarketing: how brands are manipulating your brain?
A process called neuromarketing blends marketing with neuroscience. Also discusses how consumer behavior is impacted by the marketing system and how the human brain responds to it. It influences consumer behavior, feelings, and decision-making. It examines how the brain processes and reacts to marketing-related stimuli like branding, packaging, and product design. To learn how the brain reacts to various marketing stimuli, neuromarketing strategies can utilize eye tracking, biometric tests, and brain imaging instruments like fMRI and EEG.
#Neuromarketing:how brands are manipulating your brain#Neuromarketing#Importance of neuromarketing#What are the neuromarketing techniques#What are the objectives of neuromarketing#Functional Magnetic Resonance Imaging (fMRI)#Electroencephalogram (EEG)#Eye tracking#Biometric sensors#The Implicit Association Test (IAT)#Understanding consumer behavior#Improving product design#Enhancing brand perception#Increasing advertising effectiveness#Maximizing customer satisfaction#benefits of neuromarketing#marketing#neuro#what is neuromarketing#neuromarketing tips#neuromarketing reviews#neuromarketing summary
2 notes
·
View notes
Text
What are Biometrics?
Since the 1980s, biometrics has been used in fingerprint identification. When comparing collected fingerprints from crime scenes to registered fingerprints of persons in databases, automated fingerprint identification systems (AFIS) assist investigators.
(more…)

View On WordPress
#biometrics#biometrics and forensic science#how safe is biometric identification#what are biometrics#what are biometrics characteristics#what are the types of biometrics#what are the uses of biometrics#what is the example of biometric security#what is the uses of biometrics in forensic science
2 notes
·
View notes
Text
I think I personally could get rid of ulf kristersson just by walking up to him in completely flat shoes and standing straight in front of him and staring down at him . he’d be crying in just a few short minutes if not less
#he’s like…the stereotype of a short man who can’t stand that he’s short and compensates by threatening people and being loud and greedy#I hope he **** he’s tRASH!!!!#promising a holocaust survuvor to never collaborate with the neo nazi party except that exactly what he did#saying they’re gonna collect biometric data of ~non European immigrants~#massively shrinking the already too small refugee and visa q uota etc#(and yeah we all remember the campaign ad he did in hunting gear about ‘guarding the borders’)#putting a nuclear power plant logo on Ukraine’s flag in another campaign because in order for sweden to be free from Russian influence we#need more nuclear power? this was done like days after russia first arrived at zaporizhia nuclear power plant btw#and now they’re shutting down the ministry of climate too#like I just need him to ***#also about the height thing like he made the Christian democrat party leader whom I also despise#who is taller than him and a woman stand below him on a staircase for some campaign pictures#after he’s teared up I tell him I’m actually only 7 cm taller than the average Swedish woman so really nothing extraordinary#their current plans are just let’s throw out refugees and starve all the poor people#while the planet is on all sorts of fire and we’re not gonna do anything about it uwu#anyway I want to see him break down completely#and piss off#and take his entire cabinet and sverigedemokraterna with him
1 note
·
View note
Text
I cannot express emphatically enough how much I hate requirements to sign in, in this case signing into a microsoft account to set up windows.
Seriously what the fuck do you need this for. Just give me a local account. Why the fuck do I need to be internet connected. Is it because you're bad engineers and designers? Well, yes. But also is it because you're trying to hold me and my data captive through monopolistic practices and surveillance which is also used to push ads and steal my data? Why yes.
Every time I touch one of these disgusting products I feel like flying out to Seattle, breaking into the microsoft building, and covering every surface in gorilla glue.
#it inspires violence#truly fuck you of you force me to connect to the internet for your software to work#it also forces a pin?#like what the fuck this is so insecure#you're trying to force biometrics and reducing password security to a pin#fucking die#I'll add your mouth and nose to the surfaces I'm gorilla gluing#and there's ads in my operating system#seriously i will flense you microsoft#every single one of you one by one
0 notes
Text
Exploring the Future of Security: A Deep Dive into Biometric Authentication Systems!

In the realm of security, advancements in technology have continually pushed the boundaries of what's possible. One such innovation that has garnered significant attention is biometric authentication. Gone are the days of relying solely on passwords or PINs; biometric authentication systems offer a more secure and convenient way to verify identity. In this series of articles, we'll explore the intricacies of biometric authentication systems, from their fundamental principles to their real-world applications and future prospects.
Types of Biometric Authentication
Biometric authentication encompasses various methods for verifying an individual's identity based on unique physiological or behavioral characteristics. From widely recognized fingerprint recognition to sophisticated facial recognition technology, biometric systems leverage a range of modalities to authenticate users securely.
How Biometric Authentication Works
At the heart of biometric authentication lies the process of capturing, storing, and matching biometric data. Whether it's the intricate patterns of a fingerprint or the distinct features of an iris, biometric sensors, and algorithms work in tandem to ensure accurate identification while safeguarding sensitive information.
Benefits of Biometric Authentication
The adoption of biometric authentication brings forth a multitude of benefits. Beyond enhancing security measures, biometric systems offer unparalleled convenience and user experience, reducing reliance on cumbersome passwords and mitigating the risks associated with credential-based authentication methods.
Challenges and Limitations
Despite its promise, biometric authentication is not without its challenges. Privacy concerns loom large, as the collection and storage of biometric data raise questions about individual rights and data protection. Moreover, the susceptibility to spoofing attacks and the high implementation costs present significant hurdles for widespread adoption.
Applications of Biometric Authentication
From access control systems to mobile devices and financial transactions, the applications of biometric authentication span across various industries and sectors. Whether it's streamlining time and attendance tracking or bolstering border control measures, biometric technology plays a pivotal role in shaping the future of security.
Future Trends and Developments
Looking ahead, the future of biometric authentication holds immense promise. With advancements in technology, we can expect to see greater integration with artificial intelligence and machine learning, paving the way for more sophisticated and resilient authentication systems. Moreover, emerging biometric modalities and their applications in fields like healthcare and retail hint at a future where identity verification is seamlessly woven into the fabric of everyday life.
Case Studies and Examples
Real-world implementations of biometric authentication offer valuable insights into its efficacy and impact. From multinational corporations to government agencies, organizations worldwide are leveraging biometric technology to enhance security measures and streamline operations. By examining these case studies, we can glean valuable lessons and best practices for successful deployment.
Best Practices for Implementing Biometric Authentication
As organizations embrace biometric authentication, it's essential to adhere to best practices to ensure its effective implementation. From implementing robust security measures to educating users about the technology's capabilities and limitations, a proactive approach is key to maximizing the benefits of biometric authentication while mitigating potential risks.
Conclusion
In conclusion, biometric authentication systems represent a significant leap forward in the realm of security. By harnessing the unique characteristics of individuals, these systems offer a secure, convenient, and reliable means of identity verification. As technology continues to evolve, so too will the capabilities of biometric authentication, ushering in a future where security is not just a necessity but a seamless part of our daily lives.
Through this series of articles, we aim to provide a comprehensive understanding of biometric authentication systems, empowering readers to navigate the evolving landscape of security with confidence and insight. Join us on this journey as we unravel the complexities and possibilities of biometric authentication in the digital age.
#biometric authentication#biometric authentication system#biometrics#biometric technology#biometric face recognition#technology#future of biometrics#what is biometric authentication
1 note
·
View note