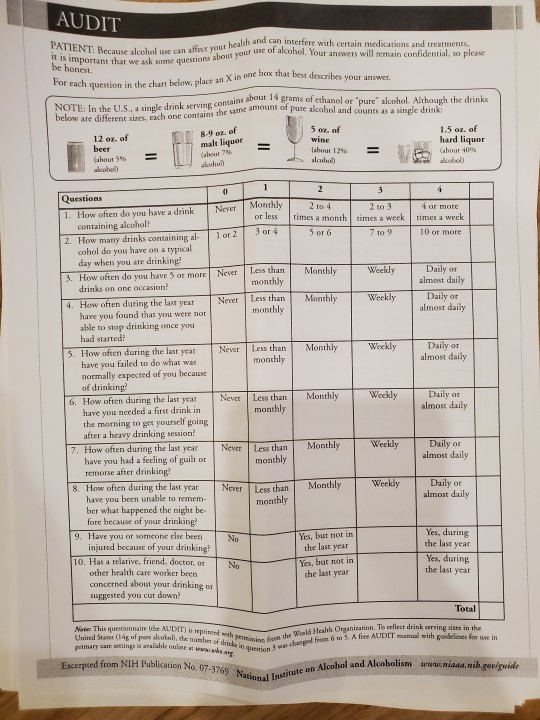
#Dast
Text

SO TRUE, LOGHAIN
#ahead of his time#op#dragon age#this is a tweet about the english monarchy#stolen throne#loghain mac tir#dast
17 notes
·
View notes
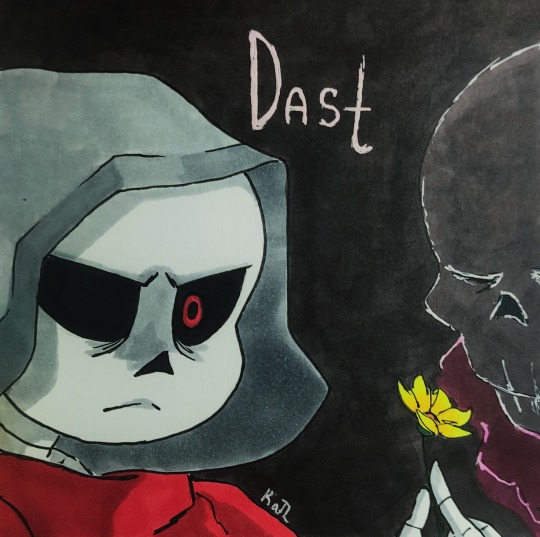
Text
hey friends
i have. a Secret.
yes... that is the first scene of the next chapter of Drinks and Subtle Things. Am I going to finish it? who knows. 🙃
15 notes
·
View notes
Photo

’Lynn Landscape’
Work by DAST for the 2021 edition of Beyond Walls. Lynn, MA.
#dast#dastuno#beyondwalls#mural#art#streetart#streetartboston#bostonstreetart#lynn#lynnma#urbanart#publicart#impermanentart
11 notes
·
View notes
Text
Quick Sketch

#artwork#art#artdrawing#sans#undertale#undertale sans#au undertale#sketch#sans au#undeverse#dasttale#dastau#dast#Dast sans
6 notes
·
View notes
Text

#Service AC Surabaya timur Ondemand 085-171-171-501#Service AC Surabaya timur Onedemand ingin memberikan tips untuk kalian yang ingin membersihkan AC kalian sendiri Sebelum mulai#pastikan AC dalam keadaan mati. Selanjutnya#siapkan alat yang diperlukan untuk membersihkan AC kalian:#sikat gigi bekas#kemoceng#obeng#cairan pembersih#penyedot debu (vacuum cleaner)#air secukupnya#dan#lap.#serviez.com#085-171-171-501#Terlihat dari persiapan pembersihan mandiri saja sudah terihat ribet#nah Sekarang anda tidak perlu pusing karena kami akan membantu mengatasi permasalahan anda. Kami adalah penyedia Jasa Servis AC di SURABAYA#MURAH dan TERPERCAYA.#Apapun merk AC anda tidak menjadi masalah karena kami melayani semua merk AC seperti Akira#Chang Hong#Dast#Gree#LG#Mitsubishi#Samsung#Sanken#Sanyo#Sharp#TCL#Toshiba#Panasonic
2 notes
·
View notes
Text
Club Furies Premiere: Dast (Italy) - Dancing Somebody [Illegal Alien Records]
Mexican label Illegal Alien Records is pleased to welcome back Dast to the label. After his last contribution to our latest V.A. compilation, Deported Series: Eleven, for which by the way we had the premiere of this Italian producer’s track, now Dast makes his debut on Illegal Alien Records with a great four-track EP titled Nebula. Another fantastic release from the Italian artist in which…

View On WordPress
#Breaks#CF Premiere#club furies#Club Furies Premiere#Dancing Somebody#Dast#Dast (Italy)#Electronic#Electronica#Grovvy Techno#IAR357#Illegal Alien Records#Italy#Napoly#Nebula#No Place All Places#Premiere#rave#techno#Worldwide
1 note
·
View note
Text
Application security testing is crucial to ensure the code is resilient to vulnerabilities. When it comes to choosing the correct methodology to application security testing the SAST Vs. DAST debate gets sparked. Both the SAST and the DAST approach detect different types of vulnerabilities. This article intends to build an understanding of when to adopt which.
#technology#digital transformation#tech#it consulting#mobile app developers#software development#technology trends#product development service#Sast#dast#static application testing#dynamic application testing#software testing#app testing#product testing
1 note
·
View note
Text

Anthony Fineran (B 1981), Southport Zhan Dast, 2023
0 notes
Photo

Kasnudeln #food #foodporn #kasnocken #kasnudeln #kärnten #carinthia #restaurant #dast #essen #foodphotography #foodstagram #foodblogger #schulgasse #tapas #austriantapas #österreichischeküche #kärntnerküche #währing #wien #vienna #igersvienna #wienliebe #wienstagram #viennablogger (hier: Währing) https://www.instagram.com/p/Cpr-EJDMpog/?igshid=NGJjMDIxMWI=
#food#foodporn#kasnocken#kasnudeln#kärnten#carinthia#restaurant#dast#essen#foodphotography#foodstagram#foodblogger#schulgasse#tapas#austriantapas#österreichischeküche#kärntnerküche#währing#wien#vienna#igersvienna#wienliebe#wienstagram#viennablogger
1 note
·
View note
Text
i'm reading the stolen throne and definitely overthinking the whole "elves have reflective eyes" thing
i looked into it, and generally, animals with reflective eyes can see better in the dark and are often nocturnal. irl there's four classifications: one seen in certain fish, marsupials, fruit bats, and crocodiles. one seen in another type of fish. one seen in cows, sheep, goats, and horses. and one seen in carnivores, rodents, and cetacea.
in the stolen throne and loghain's pov, elf eyes are described as glinting like cat eyes, so i assume elves fall into the last category, with carnivores and rodents.
i don't know enough about this stuff, but idk something about it makes me uncomfy. i can't fully figure out why? something about animalising elves? does it matter? it's almost certainly not that deep. idk, something about it squicks me out.
#maybe cause in dao theres functionally no difference physically between elves and humans apart from a slight size diff and the ears#so any new info feels like... further othering?#but i dont know why that matters even cause they ARE different#maybe because of the amount of elven prejudice?#but again its... a game#aster be normal challenge?#op#dragon age#dast
3 notes
·
View notes
Link
AI applications open new security vulnerabilities because they are complex and require much data and computing power to work correctly. As AI applications become more complex and rely on more data, the potential for security breaches increases. In addition, AI applications can be used to manipulate data, which can create new security risks. In this article, you will learn about possible further attacks on the ML model and AI-as-a-service apps and learn how to deal with them.
0 notes
Link
The newest chapter of Drinks and Subtle Things is up! Yes, that’s 2 updates in the same calendar year. You are so welcome.
7 notes
·
View notes
Text
What is the difference between DAST and SAST?
High-profile data breaches are a cause of concern for many organizations. Not only is valuable data lost, but, the effort and reputation the data brings to the organization are also lost, once the data has been breached by unethical hackers.
Hence, there are certain robust security testing techniques that can be applied, which in turn can prove to provide the required security to prevent data loss or getting entangled in any untoward cyber-attack.
In this article, you will get to know the differences between static application security testing and dynamic application security testing.
What is SAST (Static Application Security Testing)?
Security vulnerabilities are identified by analyzing the program source code. These vulnerabilities include external entity (XXE) attacks, buffer overflows, SQL injection etc.
It is an open-box testing technique. The software application is scanned from the inside out to discover security vulnerabilities in the code before execution or compilation.
The developers are guided by the SAST methodology, so that application can be tested at the initial development stages without a functional component being executed.
The application source code security flaws are discovered early by this approach and security issues are avoided in later development phases. This will in turn enhance the overall program security and decrease development time.

SAST testing tools:
1. Klocwork: It is a static code analyzer for Python, JavaScript, Java, C#, C++ or C.
2. Checkmarx: Multiple programming languages are supported by this tool.
If serious security errors need to be mitigated and more secure applications need to be produced, then SAST can be incorporated by developers into their Continuous Integration and Continuous Deployment (CI/CD) pipelines. SAST can use many use cases for creating more secure applications.
What is DAST (Dynamic Application Security Testing)?
A software application is evaluated by DAST. The actions of a malicious actor are simulated by DAST, who is trying to break into the application remotely.
Real-time software applications are scanned by DAST against leading vulnerability sources like SANS/CWE 25 or OWASP Top 10 to find open vulnerabilities or security flaws.
It is a closed-box testing technique through which an outside attacker’s perspective is stimulated. The application’s inner functions may not be known to the tester.
Those security vulnerabilities that cannot be detected by SAST, such as those appearing during the program runtime are detected by DAST.
A complete working application is required by DAST that is reserved for a later phase in the application development process. The application needs to be interacted by testers, check outputs, provide inputs and simulate other actions that are typical user interactions.
These tests make sure that the specific application is not susceptible to web attacks such as SQL injection or cross-site scripting (XXS).

DAST tools:
There are many commercially available DAST tools. Arachni is an open-source tool through which rich functionalities are provided. Scanning web applications are supported by Arachni’s Ruby framework for vulnerabilities.
SAST vs. DAST should be strategically decided by the team and implemented tactically in order to derive beneficial results.

Conclusion: If you are looking to implementing SAST or DAST or both for your specific project, then do get connected with a globally renowned software testing services company that will provide you with a tactical testing blueprint that is in line with your project specific requirements.
About the author: I am a technical content writer focused on writing technology specific articles. I strive to provide well-researched information on the leading market savvy technologies.
0 notes
Text
Dast
1 note
·
View note