#frauding
Text
38K notes
·
View notes
Text

Man just doesn't stop fucking MURDERING white men who've done very shitty things
Edit: Yes I'm aware that Hbomb wasn't really The Guy to take down Wakefield, and Wakefield was gotten by Deere, however it was for the meme
Edit two: When referring to Shapiro I was talking about the Aquaman clip
#hbomberguy#cassie rambles#he got bencil chaperone for being FUCKING STUPID#he got andrew wakefield for being LITERALLY THE FUCKING WORST#he got tommy tallarico for being a COMPLETE FUCKING FRAUD#and now he's gotten james somerton for being a massive fucking plagiarist#AND HE'S TOPPED THE VIDEO OFF THROUGH DONATING ALL THE MONEY TO THE ACTUAL CREATORS AND SHOUTING OUT QUEER CREATORS!!!!#GODDD HBOMB YOU. YOU GODDAMN.#BIG FUCKING SHOUTOUT
26K notes
·
View notes
Text
i will never understand why more people in their 80s don't commit felonies. you reach that age and surely there's something illegal you always wanted to do but didn't bc Consequences
dammit, GO FORTH GRANNIES!!! rob an armored car! hold up that bank! tunnel your way into fort knox! what are they gonna do, sentence you to 20 years? good fuckin luck with that
#mine would be a coordinated museum heist utilizing the lifetimes of experience and diverse expertise of my fellow nursing home residents#also there's Karl the orderly. his skill is he drives the shuttle van#technically he shouldn't be enabling us but he thinks it's a good enrichment activity#heck debra hasn't been this excited since her son flew in from australia.#plus Karl figures formulating an elaborate heist is better brain exercise than the puzzle books they keep in the resident lounge#all the sudokus are half finished anyway#update: upon consideration my second choice is just. MASSIVE credit card fraud.
17K notes
·
View notes
Text
How I got scammed

If you'd like an essay-formatted version of this post to read or share, here's a link to it on pluralistic.net, my surveillance-free, ad-free, tracker-free blog:
https://pluralistic.net/2024/02/05/cyber-dunning-kruger/#swiss-cheese-security

I wuz robbed.
More specifically, I was tricked by a phone-phisher pretending to be from my bank, and he convinced me to hand over my credit-card number, then did $8,000+ worth of fraud with it before I figured out what happened. And then he tried to do it again, a week later!
Here's what happened. Over the Christmas holiday, I traveled to New Orleans. The day we landed, I hit a Chase ATM in the French Quarter for some cash, but the machine declined the transaction. Later in the day, we passed a little credit-union's ATM and I used that one instead (I bank with a one-branch credit union and generally there's no fee to use another CU's ATM).
A couple days later, I got a call from my credit union. It was a weekend, during the holiday, and the guy who called was obviously working for my little CU's after-hours fraud contractor. I'd dealt with these folks before – they service a ton of little credit unions, and generally the call quality isn't great and the staff will often make mistakes like mispronouncing my credit union's name.
That's what happened here – the guy was on a terrible VOIP line and I had to ask him to readjust his mic before I could even understand him. He mispronounced my bank's name and then asked if I'd attempted to spend $1,000 at an Apple Store in NYC that day. No, I said, and groaned inwardly. What a pain in the ass. Obviously, I'd had my ATM card skimmed – either at the Chase ATM (maybe that was why the transaction failed), or at the other credit union's ATM (it had been a very cheap looking system).
I told the guy to block my card and we started going through the tedious business of running through recent transactions, verifying my identity, and so on. It dragged on and on. These were my last hours in New Orleans, and I'd left my family at home and gone out to see some of the pre-Mardi Gras krewe celebrations and get a muffalata, and I could tell that I was going to run out of time before I finished talking to this guy.
"Look," I said, "you've got all my details, you've frozen the card. I gotta go home and meet my family and head to the airport. I'll call you back on the after-hours number once I'm through security, all right?"
He was frustrated, but that was his problem. I hung up, got my sandwich, went to the airport, and we checked in. It was total chaos: an Alaska Air 737 Max had just lost its door-plug in mid-air and every Max in every airline's fleet had been grounded, so the check in was crammed with people trying to rebook. We got through to the gate and I sat down to call the CU's after-hours line. The person on the other end told me that she could only handle lost and stolen cards, not fraud, and given that I'd already frozen the card, I should just drop by the branch on Monday to get a new card.
We flew home, and later the next day, I logged into my account and made a list of all the fraudulent transactions and printed them out, and on Monday morning, I drove to the bank to deal with all the paperwork. The folks at the CU were even more pissed than I was. The fraud that run up to more than $8,000, and if Visa refused to take it out of the merchants where the card had been used, my little credit union would have to eat the loss.
I agreed and commiserated. I also pointed out that their outsource, after-hours fraud center bore some blame here: I'd canceled the card on Saturday but most of the fraud had taken place on Sunday. Something had gone wrong.
One cool thing about banking at a tiny credit-union is that you end up talking to people who have actual authority, responsibility and agency. It turned out the the woman who was processing my fraud paperwork was a VP, and she decided to look into it. A few minutes later she came back and told me that the fraud center had no record of having called me on Saturday.
"That was the fraudster," she said.
Oh, shit. I frantically rewound my conversation, trying to figure out if this could possibly be true. I hadn't given him anything apart from some very anodyne info, like what city I live in (which is in my Wikipedia entry), my date of birth (ditto), and the last four digits of my card.
Wait a sec.
He hadn't asked for the last four digits. He'd asked for the last seven digits. At the time, I'd found that very frustrating, but now – "The first nine digits are the same for every card you issue, right?" I asked the VP.
I'd given him my entire card number.
Goddammit.
The thing is, I know a lot about fraud. I'm writing an entire series of novels about this kind of scam:
https://us.macmillan.com/books/9781250865878/thebezzle
And most summers, I go to Defcon, and I always go to the "social engineering" competitions where an audience listens as a hacker in a soundproof booth cold-calls merchants (with the owner's permission) and tries to con whoever answers the phone into giving up important information.
But I'd been conned.
Now look, I knew I could be conned. I'd been conned before, 13 years ago, by a Twitter worm that successfully phished out of my password via DM:
https://locusmag.com/2010/05/cory-doctorow-persistence-pays-parasites/
That scam had required a miracle of timing. It started the day before, when I'd reset my phone to factory defaults and reinstalled all my apps. That same day, I'd published two big online features that a lot of people were talking about. The next morning, we were late getting out of the house, so by the time my wife and I dropped the kid at daycare and went to the coffee shop, it had a long line. Rather than wait in line with me, my wife sat down to read a newspaper, and so I pulled out my phone and found a Twitter DM from a friend asking "is this you?" with a URL.
Assuming this was something to do with those articles I'd published the day before, I clicked the link and got prompted for my Twitter login again. This had been happening all day because I'd done that mobile reinstall the day before and all my stored passwords had been wiped. I entered it but the page timed out. By that time, the coffees were ready. We sat and chatted for a bit, then went our own ways.
I was on my way to the office when I checked my phone again. I had a whole string of DMs from other friends. Each one read "is this you?" and had a URL.
Oh, shit, I'd been phished.
If I hadn't reinstalled my mobile OS the day before. If I hadn't published a pair of big articles the day before. If we hadn't been late getting out the door. If we had been a little more late getting out the door (so that I'd have seen the multiple DMs, which would have tipped me off).
There's a name for this in security circles: "Swiss-cheese security." Imagine multiple slices of Swiss cheese all stacked up, the holes in one slice blocked by the slice below it. All the slices move around and every now and again, a hole opens up that goes all the way through the stack. Zap!
The fraudster who tricked me out of my credit card number had Swiss cheese security on his side. Yes, he spoofed my bank's caller ID, but that wouldn't have been enough to fool me if I hadn't been on vacation, having just used a pair of dodgy ATMs, in a hurry and distracted. If the 737 Max disaster hadn't happened that day and I'd had more time at the gate, I'd have called my bank back. If my bank didn't use a slightly crappy outsource/out-of-hours fraud center that I'd already had sub-par experiences with. If, if, if.
The next Friday night, at 5:30PM, the fraudster called me back, pretending to be the bank's after-hours center. He told me my card had been compromised again. But: I hadn't removed my card from my wallet since I'd had it replaced. Also, it was half an hour after the bank closed for the long weekend, a very fraud-friendly time. And when I told him I'd call him back and asked for the after-hours fraud number, he got very threatening and warned me that because I'd now been notified about the fraud that any losses the bank suffered after I hung up the phone without completing the fraud protocol would be billed to me. I hung up on him. He called me back immediately. I hung up on him again and put my phone into do-not-disturb.
The following Tuesday, I called my bank and spoke to their head of risk-management. I went through everything I'd figured out about the fraudsters, and she told me that credit unions across America were being hit by this scam, by fraudsters who somehow knew CU customers' phone numbers and names, and which CU they banked at. This was key: my phone number is a reasonably well-kept secret. You can get it by spending money with Equifax or another nonconsensual doxing giant, but you can't just google it or get it at any of the free services. The fact that the fraudsters knew where I banked, knew my name, and had my phone number had really caused me to let down my guard.
The risk management person and I talked about how the credit union could mitigate this attack: for example, by better-training the after-hours card-loss staff to be on the alert for calls from people who had been contacted about supposed card fraud. We also went through the confusing phone-menu that had funneled me to the wrong department when I called in, and worked through alternate wording for the menu system that would be clearer (this is the best part about banking with a small CU – you can talk directly to the responsible person and have a productive discussion!). I even convinced her to buy a ticket to next summer's Defcon to attend the social engineering competitions.
There's a leak somewhere in the CU systems' supply chain. Maybe it's Zelle, or the small number of corresponding banks that CUs rely on for SWIFT transaction forwarding. Maybe it's even those after-hours fraud/card-loss centers. But all across the USA, CU customers are getting calls with spoofed caller IDs from fraudsters who know their registered phone numbers and where they bank.
I've been mulling this over for most of a month now, and one thing has really been eating at me: the way that AI is going to make this kind of problem much worse.
Not because AI is going to commit fraud, though.
One of the truest things I know about AI is: "we're nowhere near a place where bots can steal your job, we're certainly at the point where your boss can be suckered into firing you and replacing you with a bot that fails at doing your job":
https://pluralistic.net/2024/01/15/passive-income-brainworms/#four-hour-work-week
I trusted this fraudster specifically because I knew that the outsource, out-of-hours contractors my bank uses have crummy headsets, don't know how to pronounce my bank's name, and have long-ass, tedious, and pointless standardized questionnaires they run through when taking fraud reports. All of this created cover for the fraudster, whose plausibility was enhanced by the rough edges in his pitch - they didn't raise red flags.
As this kind of fraud reporting and fraud contacting is increasingly outsourced to AI, bank customers will be conditioned to dealing with semi-automated systems that make stupid mistakes, force you to repeat yourself, ask you questions they should already know the answers to, and so on. In other words, AI will groom bank customers to be phishing victims.
This is a mistake the finance sector keeps making. 15 years ago, Ben Laurie excoriated the UK banks for their "Verified By Visa" system, which validated credit card transactions by taking users to a third party site and requiring them to re-enter parts of their password there:
https://web.archive.org/web/20090331094020/http://www.links.org/?p=591
This is exactly how a phishing attack works. As Laurie pointed out, this was the banks training their customers to be phished.
I came close to getting phished again today, as it happens. I got back from Berlin on Friday and my suitcase was damaged in transit. I've been dealing with the airline, which means I've really been dealing with their third-party, outsource luggage-damage service. They have a terrible website, their emails are incoherent, and they officiously demand the same information over and over again.
This morning, I got a scam email asking me for more information to complete my damaged luggage claim. It was a terrible email, from a noreply@ email address, and it was vague, officious, and dishearteningly bureaucratic. For just a moment, my finger hovered over the phishing link, and then I looked a little closer.
On any other day, it wouldn't have had a chance. Today – right after I had my luggage wrecked, while I'm still jetlagged, and after days of dealing with my airline's terrible outsource partner – it almost worked.
So much fraud is a Swiss-cheese attack, and while companies can't close all the holes, they can stop creating new ones.
Meanwhile, I'll continue to post about it whenever I get scammed. I find the inner workings of scams to be fascinating, and it's also important to remind people that everyone is vulnerable sometimes, and scammers are willing to try endless variations until an attack lands at just the right place, at just the right time, in just the right way. If you think you can't get scammed, that makes you especially vulnerable:
https://pluralistic.net/2023/02/24/passive-income/#swiss-cheese-security

Image:
Cryteria (modified)
https://commons.wikimedia.org/wiki/File:HAL9000.svg
CC BY 3.0
https://creativecommons.org/licenses/by/3.0/deed.en
10K notes
·
View notes
Text

surprise it's yuri!!!in 2024
#my art#yuri on ice#yuri!!! on ice#yoi#fanart#katsuki yuuri#victor nikiforov#victuuri#yoi fanart#this was the secret 4th thing that lost the poll jdsfgsdfjj#id been thinking about doing a tribute since getting that one ask but i didn't anticipate how Into it i would get once i started#the way i flew through this piece .. just over 1 day??? insane#yuri is /that/ ingrained in my muscle memory#I was looking at refs and ?? id forgotten how wild this show was#we just got all of that?? a pole dance a proposal a kiss a pair skate....and it was ALL canon? incredible#AND YEAH UNPROMPTED HISTORY MAKER PLAYS IN MY YT MIX#dean fujioka jumpscare#also looking back at my old yoi pieces was so wild. that ws really 8 years ago huh.#little bit of an ego boost looking at how far ive come#but also im just grateful idk sry 2 b sappy on main#i hope 16 year old me is happy that i did this bc im happy i did this#edit bc i forgot a bunch of white outline i am a fraud
7K notes
·
View notes
Text
He should of course be in jail, but we can surely lament that America will never have a congressman this hilarious again.
9K notes
·
View notes
Text
It’s a bit unrealistic how Toph never made any counterfeit coins once she learned to metalbend
#I mean it would probably be a bit controversial for a children’s show to demonstrate one of their main characters committing fraud#but like come on#toph beifong#atla toph#atla#meta
3K notes
·
View notes
Text

game night pt. 2: the return of tim
#wayne family adventures#batman#batfam#dick grayson#jason todd#alfred pennyworth#stephanie brown#duke thomas#cassandra cain#damian wayne#timothy wayne#meme#draw the squad meme#princeorcaart#the return of tim after a brutal defeat#of course it's a capatilistic hellscape game lmao#this was the true battle of the cowl hahaha#dick accidentally committed tax fraud and ended up in jail
6K notes
·
View notes
Text
Tried to tip a tumblr blog at 1am and it was such a suspicious transaction it immediately put a full fraud freeze on my account
Fortunately, banks no longer just ask 'did you make that transaction' they want to make sure you weren't scammed into making that transaction and 5mins after their call will give away all your money anyway.
This is an honest to goodness life saving movement and I cannot be happier banks are adopting it
Unfortunately, it meant I had to have the most embarrassing financial call of my life
-
Me: Ah yeah I was just trying to tip a tumblr blog
Cash: right and were you directed there by a Facebook link? An Instagram advert?
Me: no I was just on tumblr...on purpose
-
Caah: and this person asked you for money?
Me: oh no they just had a funny story, which happened to be about money and I thought, "wouldn't it be funny if I tipped them"
-
Me: * covering a reblog by reblog update on the adventures my mutual was having *
Cash: okay I don't think that can actually happen though..
Me: It might not have, but i was happy to tip them just because it was funny
-
Cash: and how well do you think you know this person?
Me: *considers explaining how much I know about a beloved mutual without ever knowing their name or face* ... I have no idea who this person is
I think in the end Cash decided there was no saving me from myself
#Chase unblocked my card#But I did not come off well#But this is a good thing!#Be fraud aware!#Tipping a blog should be like handing money to someone in the street#Only do it if you can afford it and WANT TO and do not care what it goes on#It COULD be a scam#You've got to be alright with that#YOU DO NOT KNOW THESE PEOPLE#THE VET BILL ASKS ARE A SCAM#scams
3K notes
·
View notes
Text

Aromantic pride flag colorpicked off of the aromantic pride flag
#aro#aromantic#arospec#i'm a fraud this is just an aromantic pride flag i didn't colorpick a damn thing
3K notes
·
View notes
Text
🚨WARNING!🚨 AZA-accredited zoos and aquariums across the U.S. are being targeted with scams advertising fake tickets at discounted prices.
Scammers are targeting Monterey Bay Aquarium visitors with these fake ticket offers online.
The only place to purchase official Aquarium tickets is through our website. As a nonprofit organization, proceeds from legitimate ticket sales allow us to continue our mission of inspiring conservation of the ocean. Find out more here: https://mbayaq.co/3vlcRpi

2K notes
·
View notes
Text
source 1
source 2
source 3
#destiel meme news#destiel meme#news#united states#us news#us politics#donald trump#fuck trump#trump organization#anti trump#trump family#trump fraud#trump civil fraud trial#fraud trial#new york#judge engoron#arthur engoron#judge arthur engoron#get fucked idiot
2K notes
·
View notes
Text
The Victor Ninov situation is one of my favourite cases of scientific fraud because it's rare to see so straightforward an example of someone being brought low by their own hubris.
Like, okay, faking the synthesis of a previously unobserved element: it's one of the few varieties of scientific fraud that actually has a clear gameplan for getting away with it. The physical properties of unobserved elements are, in principle, predictable, and there are only so many ways to go about synthesising them. If you do your homework, it's not outside the realm of possibility that your claimed results will end up being at least mostly consistent with the results of subsequent legitimate efforts to synthesise that element, and any minor discrepancies will end up being dismissed as statistical anomalies and/or the product of sloppy experimental design. It's by no means an easy game to play, but it's a game you can conceivably win.
And Victor Ninov did it. He rolled the dice and he won – twice. His fabricated results for elements 110 and 112 were corroborated by later work, and nobody noticed that his actual data was a crock of shit. He got away with it as cleanly as he could have hoped. It was only the third time he tried it, with element 118, that he biffed it and claimed results which nobody could replicate, and this is the only reason his earlier frauds were discovered. If he'd quit while he was ahead, it's likely the first two incidents never would have come to light.
Like, they say the third time's the charm, and buddy here learned the hard way that sometimes, the opposite also holds true.
2K notes
·
View notes
Text
Canonical enshittification

This is the Facebook playbook: you lure in publishers by promising them a traffic funnel ("post excerpts and links and we'll show them to people, including people who never asked to see them"), and then the rug-pull: "Post everything here, don't link to your own site. Become a commodity supplier to our platform. Abandon all your own ways of making money. Become entirely subject to the whims of our recommendation system."
Next will be: "We block links to other sites because they might be malicious."
Then some kind of "pivot to video."
Probably not video (though who knows?) but some other feature that a major rival has, which Twitter will attempt to defraud its captive, commodified suppliers into financing an entry into.
In case you were wondering, yes, this is canonical enshittification. Lure in business customers (publishers) by offering surpluses (algorithmic recommendation and an ensuing traffic funnel). Lock them in (by capturing their audience and blocking interop and logged-out reading).
Then rug the publishers, clawing back all the surpluses you gave them and more, draining them of all available capital and any margins they have, until they die or bite the bullet and leave.
I would also give good odds on this leading to a revivification of the "Pay us tens of thousands of dollars a month for a platinum checkmark and we'll actually show what you post to the people who asked to see it."
That will be pitched as the answer to publishers' complaints about not wanting to turn themselves into commodity Twitter inputs. It will be priced at the same (or more) as the revenues publishers expect to lose from being commodified, making it a wash.
All of this seems to me to be an "unfair and deceptive business practice" under Sec 5 of the FTC Act.
If I sign up to follow you because I want to see what you post, and Twitter shadowbans your posts unless they are formatted to maximize your dependence on Twitter, they have deceived me, and are being unfair to you.
This is *very* analogous to the Net Neutrality debate, where a platform blocks or deprioritizes the things its users ask to see, based on whether the suppliers of those things are its competitors.
I've written about how an end-to-end principle for social media could be enforced under Sec 5 of the FTCA, how it would address this kind of sleazy practice, how it would be easy to administer, and wouldn't form a barrier to entry for new market entrants:
https://pluralistic.net/2022/12/10/e2e/#the-censors-pen
7K notes
·
View notes
Text
now that it's been five months, can I point out something really funny that I don't think anybody noticed?
so you may remember that round 2 was notorious for the voter fraud that happened in blackbonnet vs stucky. some people (on both sides!) found the whole thing hilarious; some people (again, on both sides!) got really, really unreasonably angry.
the graph looked like this. now, that's a very sudden and noticeable spike there at the end; this was definitely a coordinated effort and it was definitely to some degree fraud. there's screenshots of a job listing on sproutgigs to prove it.

but look at the rest of the graph. that's fairly natural-looking— no enormous spikes, no stopping and starting. there's bumps, of course, because sometimes you get reblogged by someone with lots of followers, and there's upsets, but there aren't cliffs. for the most part, except for that sudden bend at the end, this is pretty normal voter behavior.
people joked about the fraud in this poll for weeks afterwards. "hey, where's the award for most voter fraud?" people said.
well.
the award for most voter fraud does not go to stucky vs blackbonnet. it goes to this absolute fucking nonsense:
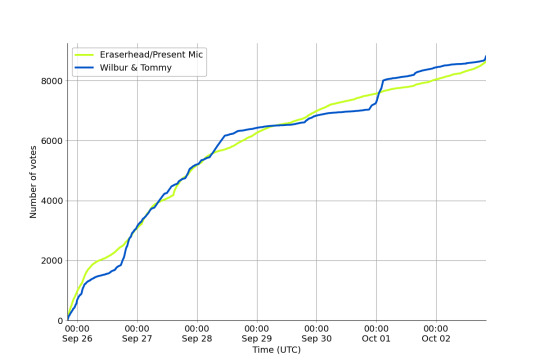
like, look at that. look at those long stretches where almost nobody was voting crimeboys. look at the sudden jumps, and look at how suddenly they end. in the earlier sections you can see the little pauses where whoever was frauding took a break to rest their wrists and get a snack.
I don't know what I think the takeaway here is. you could say this is a story about how accusations of voter fraud don't track voter fraud, they track controversy. you could say this is a story about how if you don't have a graph right in front of you, it is significantly harder to identify voter fraud than you think it is. both of those are even true.
but personally, I like to look at it as a post about how if you really try, you can chart human passion. and I think that's beautiful.
1K notes
·
View notes